Your dedicated IT department — without the overhead
RWebZ Managed IT Services give small and mid-market businesses across BC, Alberta, Yukon, NWT, and Saskatchewan access to enterprise-level IT support at a predictable monthly cost. We proactively monitor, maintain, and secure your entire IT environment — so your team can focus on running the business, not fighting technology. Our approach is straightforward: fair pricing, clear billing, ethical practices, and no long-term contracts.
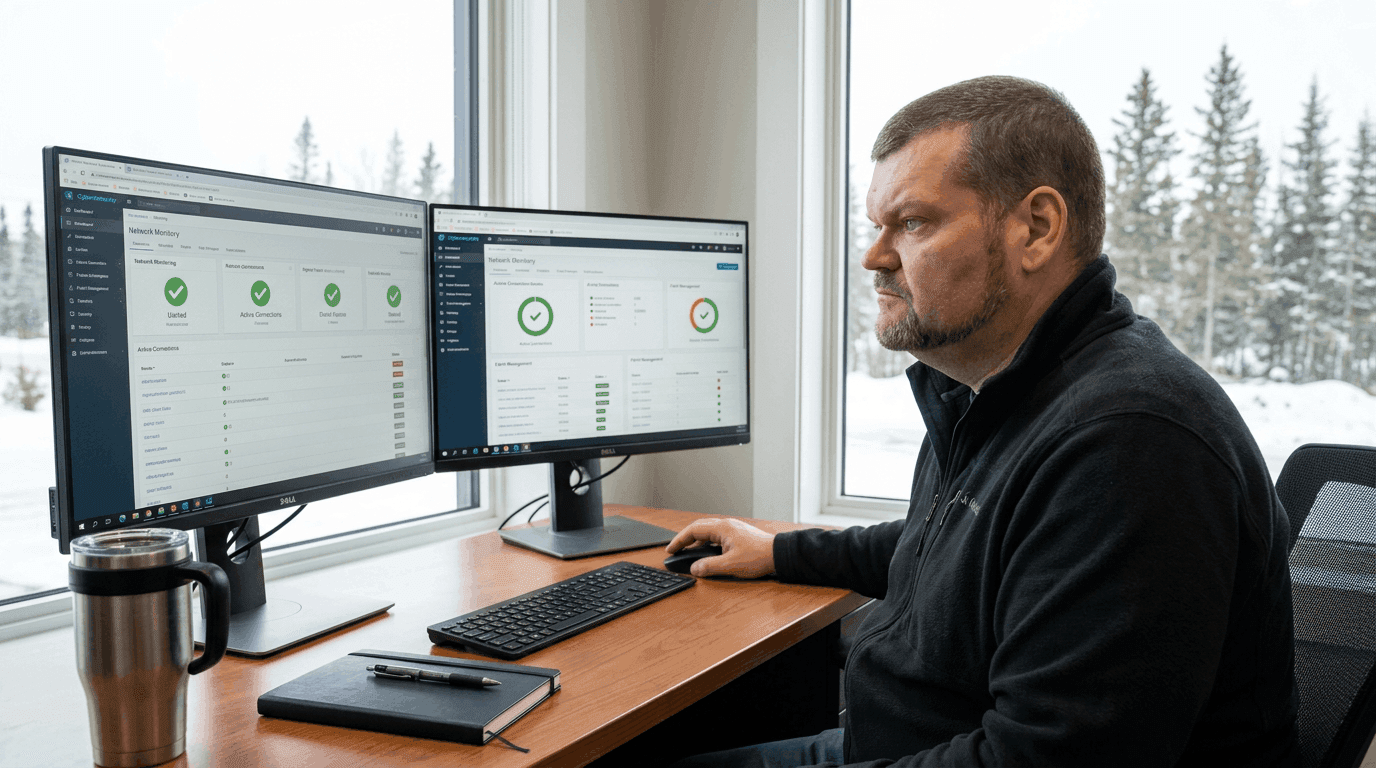
24/7 Proactive Monitoring
Continuous monitoring of your servers, workstations, mobile devices, and network infrastructure — with automated alerts and rapid response before issues become outages.
RWebZ Client Security (RCS)
Our proprietary endpoint security platform combines enterprise antivirus, packet-filtering firewall, host intrusion prevention, threat containment, and Comodo Valkyrie file verdict technology — protecting against zero-day attacks.
Patch & Update Management
Daily security patching, weekly critical updates, and monthly maintenance windows keep your systems current, compliant, and protected across all managed endpoints.
Help Desk & Remote Support
Fast, friendly remote support for your team with easy ticket submission, clear SLAs, and escalation to on-site support when needed — available across all our service regions.
How we work
Discovery & Audit
We document your full environment, identify risks and gaps, and establish baselines before any managed services begin.
Onboarding
We deploy monitoring agents, configure RCS endpoint security, set up your helpdesk portal, and define escalation paths — typically within one week.
Active Management
Ongoing monitoring, patching, maintenance, and security management — proactive, not reactive, 24 hours a day.
Monthly Reporting
A plain-language monthly report covering system health, incidents resolved, patches applied, and upcoming scheduled work.
Quarterly Reviews
We review your environment with you every quarter, identify improvements, and ensure our services continue to align with your business direction.