Your Technology Is Only as Secure as Your Weakest Point
Small and medium businesses are the most frequently targeted victims of cybercrime — not because they are the most valuable targets, but because they are often the least defended. Attackers follow the path of least resistance, and a business with outdated software, weak passwords, no endpoint protection, and no backup strategy is an open door. Understanding the threat landscape is the first step toward meaningful protection.
The Biggest Threats Facing Small and Medium Businesses Today
- Multi-factor authentication blocks 99.9% of automated account attacks
- Regular patching eliminates the majority of actively exploited vulnerabilities
- Encrypted off-site backups ensure full business continuity after any incident
- Employee security awareness training significantly reduces phishing success rates
- No single security tool provides complete protection without a layered approach
- Human error remains the leading cause of security breaches worldwide

Essential Security Practices Every Business Must Implement
Phishing attacks delivered through email remain the single most common entry point for ransomware, credential theft, and data breaches. Beyond email, vulnerabilities arise from outdated operating systems, unpatched software, unsecured Wi-Fi networks, and employees using personal devices on business networks. A single compromised credential can give an attacker access to your entire infrastructure within minutes — including client data, financial records, and communications.
60%
$4.5M
Effective cybersecurity for a small or medium business does not require enterprise-level complexity. It requires consistency and layered protection: strong password policies enforced with a password manager, multi-factor authentication on all accounts, up-to-date antivirus and endpoint detection software, regular encrypted backups stored off-site, and employee training to recognise phishing attempts. These measures address the vast majority of real-world attack vectors at a manageable cost.

How Managed IT Services Protect Your Business Proactively
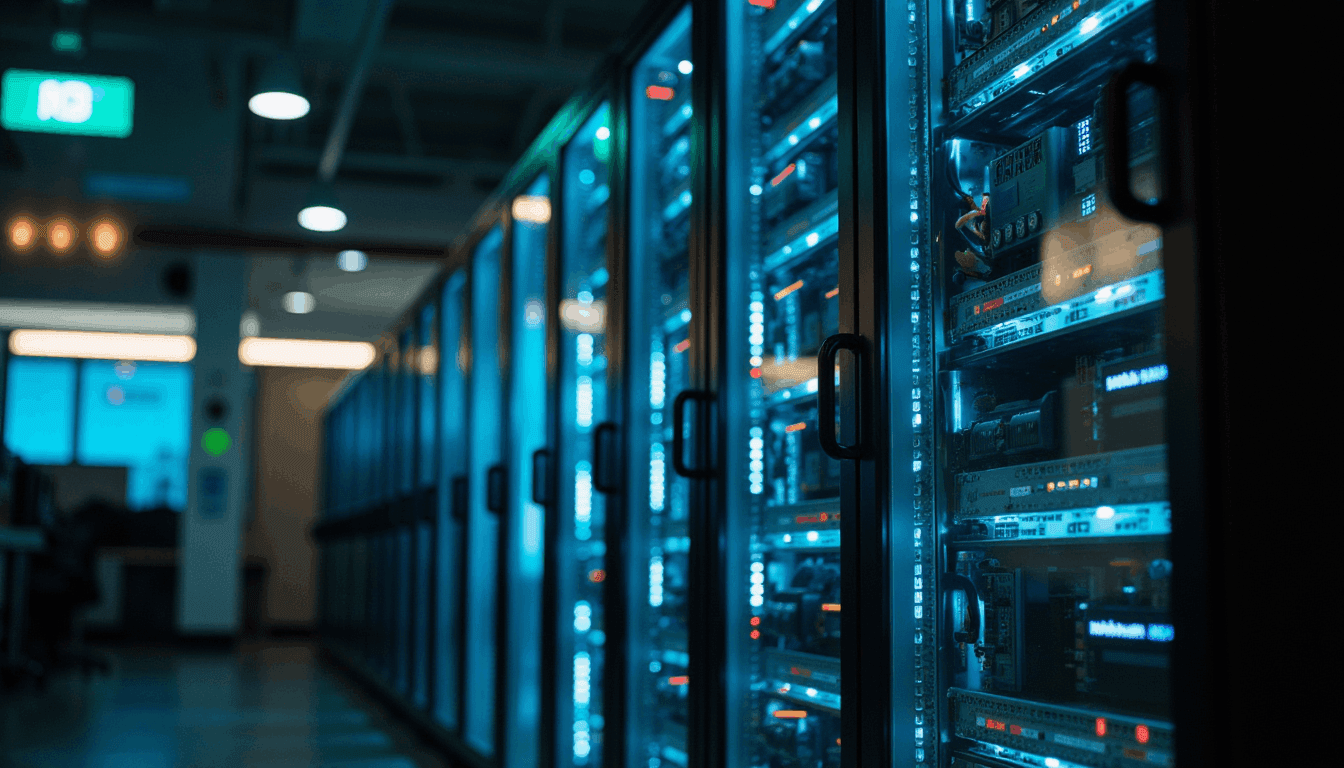
The statistics surrounding cybercrime are not abstract — they represent businesses that closed permanently, clients whose data was exposed, and owners who lost years of work in a single incident. In Canada, cybercrime costs businesses billions of dollars annually, and the Peace Region is not exempt. Remote operations, limited local IT support, and the perception that small businesses are not targets all contribute to elevated risk.
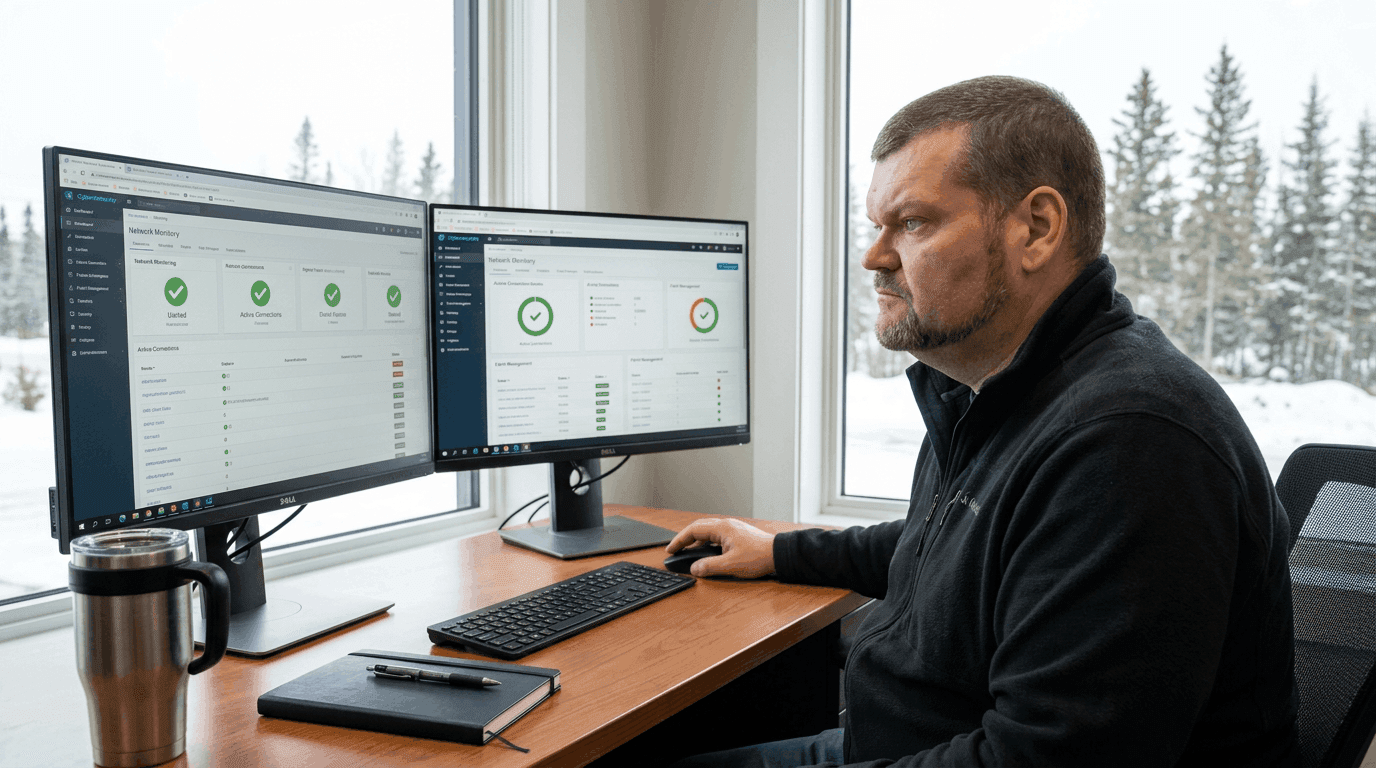
A Managed IT partner does not simply respond to problems after they occur — they proactively monitor your environment, apply patches and updates, enforce security policies, manage backups, and maintain the visibility needed to detect unusual activity before it escalates. For businesses in Northern BC operating across multiple locations or with remote teams, a fully managed security posture provides peace of mind and operational continuity that in-house approaches rarely achieve.
Don't Wait for a Breach to Act
RWebZ Group provides comprehensive managed IT and cybersecurity services for businesses across the Peace Region. From endpoint protection and backup management to firewall configuration and employee security awareness, we build and maintain the defenses your business needs to operate with confidence. Contact us to assess your current security posture.